Bucket and table permissions in Grail
powered by Grail
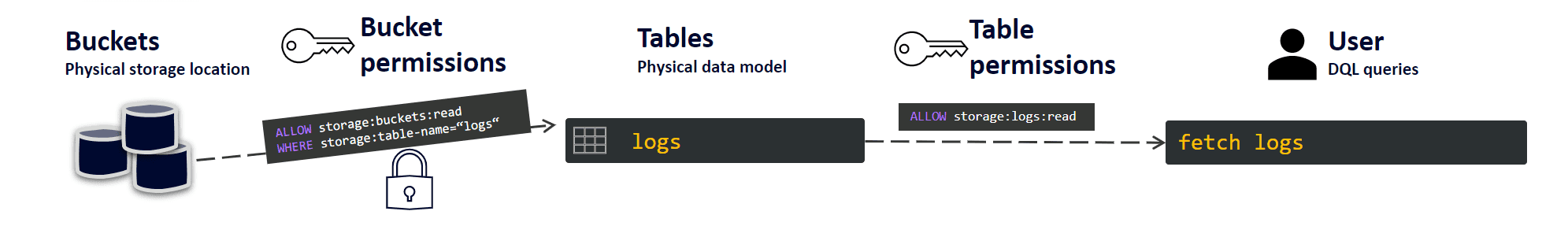
Permissions can be assigned on the bucket, table, and entity levels. Without permissions, your users cannot fetch any data from a bucket or table.
Set up permissions
To set up the bucket and table-level permissions
-
In the user menu , go to Account settings.
Shortcut: go to https://myaccount.dynatrace.com
-
Go to Identity & access management > Policies.
-
Select Create policy.
-
Add the policy details:
-
Name
-
Description
-
Policy statement—use the following format:
ALLOW <bucket permission> where <condition>; ALLOW <table permission>;See below for supported bucket and table permissions.
-
-
Select Create policy.
Supported bucket permissions
All bucket permissions need to start with storage:buckets:read. Their scope can be limited by a WHERE clause that includes one of the three operators:
-
equals,
=, indicating an exact match. -
STARTSWITHwith an expression in quotation marks. -
IN, indicating a range. -
=(equals), indicating an exact match. -
STARTSWITHwith an expression put in quotation marks. -
IN, indicating a range.
After the WHERE clause, you can filter your stored buckets by a specific bucket name or a defined table name:
- WHERE storage:bucket-name
- WHERE storage:table-name
Supported table permissions
All tables related to log monitoring have their corresponding permissions that need to be set.
| Table name | Permission |
|---|---|
logs | storage:logs:read |
events | storage:events:read |
metrics | storage:metrics:read |
bizevents | storage:bizevents:read |
spans | storage:spans:read |
entities | storage:entities:read |
dt.system.events | storage:system:read |
Choose a predefined policy
There are six predefined global policies, each set per one table (logs, events, bizevents, metrics, entities, spans), and three additional, general policies:
- Read all data
- Read default monitoring data
- Read all system data
Global policy for the logs table
This policy provides access to all logs from Grail, and narrows the bucket permission with a WHERE condition that limits the results to the log table.
This statement provides access to all built-in and custom buckets.
ALLOW storage:buckets:read WHERE storage:table-name= "logs";
ALLOW storage:logs:read;Read all data
This permission statement gives you access to all tables and all buckets, therefore it needs to be used only in justified cases.
ALLOW storage:buckets:read;
ALLOW storage:system:read,
storage:events:read,
storage:logs:read,
storage:metrics:read,
storage:entities:read,
storage:bizevents:read,
storage:spans:read;Read default monitoring data
This policy retrieves all default monitoring data.
In the first line, this policy statement gives access to all default buckets. The WHERE condition narrows the search to buckets whose name starts with default. Subsequently, the next lines list all the needed table permissions.
This statement does not give access to custom buckets.
ALLOW storage:buckets:read WHERE storage:bucket-name STARTSWITH "default_";
ALLOW storage:events:read,
storage:logs:read,
storage:metrics:read,
storage:entities:read,
storage:bizevents:read,
storage:spans:read;Read all system data
This permission statement first narrows the results to system buckets, whose name starts with dt. Then, it gives you access to all tables that contain system data, for example audit events, billing events, and query execution events. It can be useful for system admins.
ALLOW storage:buckets:read WHERE storage:bucket-name STARTSWITH "dt_";
ALLOW storage:system:read;